TL;DR
Bitwarden Premium roughly doubled in 2025–26, from about $10/year to $19.80/year. Families nudged to $47.88/year for six users. Teams stayed at $4/user/month, but the per-seat math compounds at every renewal.
If you're one person or one household, Bitwarden's paid tiers are still cheap. Stay put. This post isn't aimed at you.
For a team of 5+, a self-hosted Vaultwarden instance on managed hosting at €9/month flat (unlimited users) breaks even with Bitwarden Teams around three seats and saves roughly €350/year at ten seats.
Vaultwarden uses the official Bitwarden mobile, desktop, and browser clients. Switching is a server URL change, not a re-onboarding.
Pair Vaultwarden with 2FAuth for self-hosted TOTP. Use HashiCorp Vault for team machine secrets — database credentials, API keys, certs. Different problem, different tool.
What changed at Bitwarden in 2025–26
Bitwarden raised Premium from about $10/year to $19.80/year. Families nudged from $40/year to $47.88/year for six users. Teams held steady at $4/user/month and Enterprise at $6/user/month. The free tier still shows unlimited devices and items on the official pricing page. The renewal-cycle pain landed on per-seat plans, not the free tier.
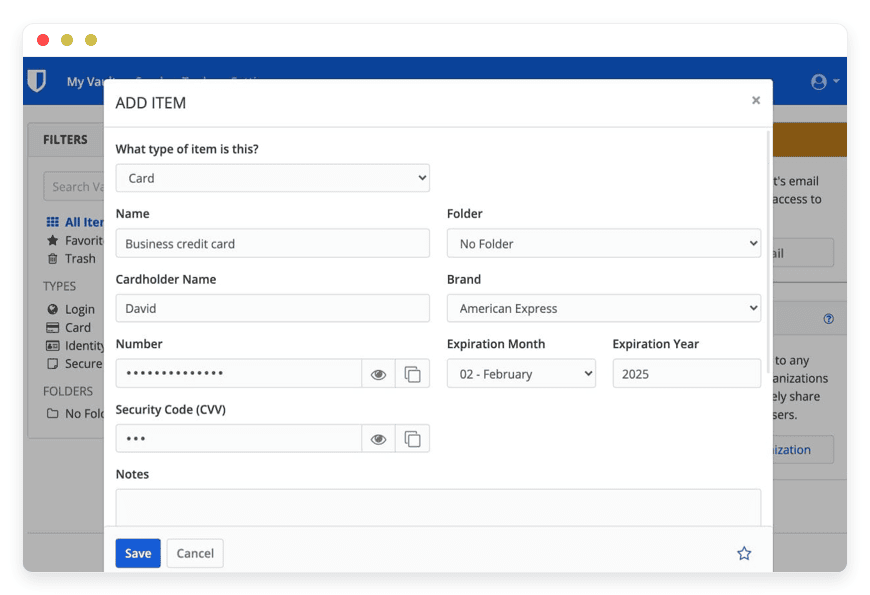
The five tiers are documented on Bitwarden's business pricing page. Free covers the basics. Premium adds an integrated TOTP authenticator, encrypted file attachments, and emergency access. Families covers six users with premium features each. Teams adds collections, audit logs, directory sync, and SCIM. Enterprise adds SSO, policies, account recovery, and a self-hosting option.
The change that matters is Premium. The single-user paid tier went from a long-running ~$10/year price to $19.80/year. That's close to a 100% increase. Families crept from $40/year to $47.88/year. Teams and Enterprise per-seat figures held. Some 2026 articles also reference unspecified free-tier changes; the live pricing page does not show a device cap. This post anchors on the verifiable price moves rather than the contested ones.
None of this makes Bitwarden a bad product. The company is open-source-friendly, audited, and well-staffed. The apps are good. The question this post answers is narrower. At what team size does the per-seat math stop adding up, and what do teams move to when it does?
Why people are leaving — the 5-seat math, not the principle
Most teams don't switch password managers because they're angry. They switch because per-seat billing scales with hiring. The renewal email arrives at quarterly close. The line item finally crosses an internal threshold. Run the Bitwarden Teams math at the scales SMB teams actually live at:
5 seats: $4 × 5 × 12 = $240/year
10 seats: $4 × 10 × 12 = $480/year
25 seats: $4 × 25 × 12 = $1,200/year
50 seats: $4 × 50 × 12 = $2,400/year
The number itself is not the problem. The slope is. A team that adds five seats in a year adds $240/year to the password-manager line. A team that doubles in a growth year doubles the line item too. Per-seat pricing is a tax on hiring. The tax compounds. The renewal email is the moment most owners notice.
The alternative most teams land on is a self-hosted Bitwarden-compatible server on flat-fee managed hosting. A managed Vaultwarden instance runs €9/month flat — €108/year — covering unlimited users on the instance. The per-seat axis disappears. Break-even with Bitwarden Teams sits around three seats. From four upward, the gap widens with every hire. At ten seats the saving is roughly €350/year. At twenty-five it's over €1,000/year.
Be honest about where this math does not work. One person on Premium pays $19.80/year. A managed Vaultwarden runs €108/year. The proprietary tier wins by a factor of five at one seat. A six-person household on Families pays $47.88/year — less than half the managed-hosting cost. If you're either of those buyers, do not switch. The post below is for the team that crossed the line where a flat fee becomes the cheaper line item.
What “alternative” actually means here
“Alternative to Bitwarden” splits three ways. The right answer depends on which split you're in. Option 1 is another proprietary password manager. Option 2 is Bitwarden's own self-hosted server. Option 3 is a self-hosted Bitwarden-compatible re-implementation. Most teams researching “alternative” actually want option 3, even if their first search query said something else.
Option 1 — another proprietary password manager.1Password Business sits at $7.99/user/month and sells a richer admin experience. Other commercial managers price below or above. The upgrade is real on a feature axis. The downgrade is that you've moved the per-seat problem one vendor over. The math at 25 seats is worse, not better.
Option 2 — Bitwarden's own self-hosted server. The official server is real software and runs the same protocol. The trade-off is operational. It ships as a multi-container deployment with MS SQL Server as the database. Full self-hosting access for an organization sits at the Enterprise tier. Resource footprint and complexity are higher than most SMB teams want to absorb.
Option 3 — a self-hosted Bitwarden-compatible re-implementation. The dani-garcia Vaultwarden project is a Rust rewrite of the Bitwarden server API. It runs the same mobile, desktop, and browser clients without changes. The footprint fits comfortably on small hardware.
The shortlist
Three open-source apps cover the password-and-secret needs that Bitwarden's paid tiers serve. Vaultwarden is the direct Bitwarden replacement. HashiCorp Vault sits next to it for team machine secrets — a related but distinct problem. 2FAuth is a self-hosted TOTP companion to use alongside Vaultwarden, not as a replacement for it.
Vaultwarden — the actual Bitwarden replacement
Stars: 58k · License: AGPL-3.0 · Latest release: 1.35.4 (Feb 2026) · Releases since 2018: 78
Vaultwarden is an unofficial Bitwarden-compatible server, written in Rust by Daniel García. It exposes the same client API as Bitwarden's own server. The official iOS app, Android app, browser extensions, and desktop clients all work against a Vaultwarden URL with no client-side changes. For a team already running Bitwarden, switching is a server URL update per user. Not a vault export, not a re-onboarding, not new training.
The project has been actively maintained since 2018. 78 releases. 494 public projects depend on the repo. One of the active maintainers is employed by Bitwarden Inc and contributes on personal time, with reviews from other maintainers. The protocol stays aligned. The rewrite isn't drifting from upstream. The maintainer pool is small but stable.
What Vaultwarden does not include is mostly the enterprise admin features. SCIM provisioning, full directory sync, the more elaborate organization policies. For a team of 5–50 that wants the Bitwarden client experience without per-seat billing, the gaps rarely matter. For a 500-person Fortune 500 with a directory-integration requirement, they do.
Best for: any team of 3+ that wants Bitwarden's UX and clients without per-seat billing.
DANIAN price: €9/month, all-in. See managed Vaultwarden hosting at €9/month.
HashiCorp Vault — for team machine secrets
License: BSL 1.1 (source-available) since August 2023 · Owner: HashiCorp, IBM-acquired Feb 2025 · OS fork: OpenBao (Linux Foundation)
Vault stores the secrets machines need. Database credentials. API keys. TLS certificates. Signing keys. Encryption keys for application data. It is not a Bitwarden replacement and does not pretend to be. A developer storing a production Postgres password reaches for Vault. A finance lead storing the company's Stripe login reaches for Vaultwarden. Different problems, different tools.
Be honest about the licensing. HashiCorp moved from MPL 2.0 to BSL 1.1 in August 2023. IBM completed its $6.4B acquisition of HashiCorp in February 2025. BSL is source-available rather than OSI-approved open-source. You can read, modify, and redistribute the code. Commercial competitive use against the HashiCorp ecosystem is restricted. The genuine OS fork is OpenBao — a Linux Foundation project that emerged after the BSL change. For SMB teams that want a stable, well-documented secrets store backed by a vendor with documentation and training, the BSL version remains the established choice. Readers who care about OSI purity above all else should know about OpenBao before they pick.
Best for: a team with a developer in-house that wants a single place for the credentials its applications and CI need.
DANIAN price: €9/month for managed Vault. See team-secret management with HashiCorp Vault.
2FAuth — self-hosted TOTP, alongside Vaultwarden
Stars: 3.8k · License: AGPL-3.0 · Latest release: v6.1.1 (March 2026)
2FAuth is a self-hosted web app for TOTP and HOTP codes. The six-digit rolling codes you've used to sign into a service that asks for a second factor. It is intentionally single-user. One person, one account, by design. Use it alongside Vaultwarden when you'd rather not keep your TOTP seeds on your phone or in the same vault as your passwords. It also gives you a desktop pane for those codes instead of unlocking your phone twenty times a day.
The reason 2FAuth shows up in a Bitwarden post: Bitwarden's integrated authenticator is a paid feature on Premium and the business plans. Buyers comparing tiers sometimes assume the only paths are pay for Premium or run a separate authenticator on their phone. 2FAuth is the third option. It solves a real day-to-day annoyance for operators who already work in a browser most of the day.
Best for: an operator who wants TOTP under personal control without the smartphone-as-single-point-of-failure pattern.
DANIAN price: €9/month for managed 2FAuth.
Comparison at 10 seats
The cleanest read on this table: ignore everything except the per-seat axis. Bitwarden Teams scales with users. The DANIAN-hosted instances do not. The math is mechanical from there. Bitwarden's annual cost grows with every hire. The flat-fee instances stay at €108/year regardless. Switching effort is low because the clients don't change.
| Bitwarden Teams (10 seats) | Vaultwarden via DANIAN | HashiCorp Vault via DANIAN | 2FAuth via DANIAN | |
| Annual cost | $480/year | €108/year | €108/year | €108/year |
| Per-seat math | $4/user/month | Flat — unlimited users | Flat — unlimited tokens | Single-user by design |
| GitHub stars | n/a (proprietary) | 58k | ~33k (BSL since 2023) | 3.8k |
License | Commercial | AGPL-3.0 | BSL 1.1 (source-available) | AGPL-3.0 |
| Switching effort from Bitwarden | n/a | Low — same clients, server-URL change | Different problem, no migration | Adjacent — TOTP companion |
Is Vaultwarden production-grade? An operator's answer
Yes, with caveats most teams can satisfy. Active maintenance with 78 releases since 2018. Latest 1.35.4 in February 2026. 494 public projects depend on the repo. The official Bitwarden clients work against it without modification. One active maintainer is employed by Bitwarden Inc and contributes on personal time. The audit history is community-driven rather than externally attested. Most of these things are easy to verify.
Maintenance velocity is real. 78 releases since 2018. The latest (1.35.4) shipped February 23, 2026. Release cadence is steady. Not weekly, but predictable enough to track upstream Bitwarden API changes without lag. The repo has 494 public dependent projects. That's the kind of long tail that catches regressions before they hit production.
Client compatibility holds. The official Bitwarden iOS app, Android app, browser extensions, and desktop clients work against a Vaultwarden server. No client-side modifications needed. The protocol is documented. The surface that matters — vault sync, send, organizations, attachments — is implemented. Breakage is rare and addressed quickly when it happens.
The “Bitwarden employee maintains Vaultwarden” fact is a credibility signal. One of the active maintainers is employed by Bitwarden Inc and contributes on personal time. Other maintainers review the code. The optics may seem strange at first read. The practical effect is that the rewrite stays aligned with the upstream protocol. Bitwarden's own teams aren't surprised by what Vaultwarden does. This isn't a hostile fork.
Audit history is community-driven. The project has had several rounds of community security review. It has a published security policy. It does not have an attested audited certification on the server itself. No open-source server does — audited certifications attach to the operator running the server, not to the codebase. If an attested certification on the password manager itself is the deal-breaker for your situation, Bitwarden's paid Enterprise tier with self-hosting will serve you better than this path will.
Running it well is real work. A production Vaultwarden needs a TLS certificate that doesn't expire. Daily off-site backups verified by restore. Not just by “the backup ran”. A monthly patch cycle on the host and the container. Monitoring for the OOM-killer and the disk fill. An SMTP relay for email. Most of that is what we run on the €9/month tier. If you'd rather operate it yourself, a developer-led team with a $24 production-class VPS can make it work. Budget a few hours a month.
How to pick — three questions to ask yourself
Three questions sort the majority of decisions cleanly. How many people will use this? Are you also storing machine secrets like database credentials and API keys? Does your situation require an attested compliance certification today? Each answer points at a different option. The work is figuring out which question is loadbearing for your situation.
1. How many people will use this? Under three: stay on Bitwarden Premium or Families. The math is on Bitwarden's side at that scale. There's no reason to add an operational concern. Three to fifty seats is where Vaultwarden via managed hosting starts winning. Above a hundred seats, the per-seat saving is enormous. Feature gaps at that scale (SCIM, more granular policies, account recovery) get heavier. The calculation becomes a real “buy vs build vs Bitwarden Enterprise self-host” review rather than a quick switch.
2. Are you also storing machine secrets? Database credentials, API keys, TLS certs, signing keys for CI. If these live in a Bitwarden vault today, that vault is doing two jobs. One of them less well. Vault belongs in the picture as a separate tool. Vaultwarden for human passwords. Vault for machine secrets. The two answer different questions and don't compete.
3. Does your situation require an attested compliance certification today? If yes, an attested certified provider serves you better. Bitwarden Enterprise self-hosting maintained by your own team carries the cert reputation. Going to a smaller managed-OSS provider for the cost saving is a poor trade-off when the sale itself depends on the cert. Run the math on the cost of the saved seats versus the cost of an audit failure. The cert wins almost every time.
FAQ
Is Vaultwarden actually compatible with the official Bitwarden apps?
Yes, fully. The same iOS app, Android app, browser extensions, and desktop clients work against a Vaultwarden server. Users change one setting — the server URL — and continue. Existing teams switch in minutes per user without re-importing the vault.
What if I want to leave Vaultwarden later — am I locked in?
No. Vaultwarden uses the same data model as Bitwarden. Each user can export through the official Bitwarden client and import elsewhere. You can also migrate the whole organisation back to Bitwarden's own server. The data belongs to the team that owns it.
How does Vaultwarden compare to Bitwarden's own self-hosted server?
The official Bitwarden self-hosted server is real and runs the same protocol. It ships as a multi-container deployment with MS SQL Server. Full org self-hosting access sits on the Enterprise tier. Vaultwarden is one Rust binary that fits on small hardware. Same clients, lower operational footprint.
Why isn't this post talking about certifications?
Because certifications are a different question from “open-source alternative”. The right answer changes the conversation. If your buyer requires an attested cert today, a compliance-certified provider is the right fit. This post is for teams making a cost-and-control trade-off, not a procurement-checklist trade-off.
Should I just self-host Vaultwarden on a $24 VPS?
Genuinely yes if you have a developer in-house. Time for monthly patching and certificate renewal. A backup-verification habit. The willingness to be the person who restores at 2am. Most SMB teams don't, which is the gap managed hosting fills. Coolify on a $24 production-class VPS is a working DIY path for the developer-led case.
What about HIBP integration and password breach checks?
Vaultwarden supports Have I Been Pwned breach checking through the same client features Bitwarden does. The calls are made by the client to the public HIBP API. Not by the server. The breach-check workflow is identical to running on Bitwarden's own server.
Is Vaultwarden free?
The software is free and AGPL-3.0 licensed. You can download it, modify it, and run it yourself at no cost. What costs money is hosting it: a server to run it on, a TLS certificate, off-site backups, monitoring, and the time to keep all of that working. Free software, paid infrastructure.
Is Vaultwarden a fork of Bitwarden?
No. Vaultwarden is a clean-room rewrite in Rust of the Bitwarden server API by Daniel García. It does not contain Bitwarden's source code. It exposes the same client API so the official Bitwarden apps work against it, but the implementation is independent.
Has Vaultwarden been security-audited?
The project has had several rounds of community security review and a published security policy. It does not have a formal third-party penetration test report on the server itself. The cryptographic primitives are from Rust's well-tested libraries. Independent security discussions exist publicly on GitHub. The codebase is small enough to audit yourself if needed.
How do I migrate from Bitwarden to Vaultwarden?
Export your Bitwarden vault as JSON from your Bitwarden account settings. Stand up a Vaultwarden server. Create your account on it through the Bitwarden client by changing the server URL. Import the JSON. Repeat for each user, or have admins import organization vaults. No data is lost.
Does Vaultwarden support passkeys?
Yes. Vaultwarden has supported passkey storage in recent releases, and the official Bitwarden clients store and use passkeys against it the same way they do against Bitwarden's own server. The server implements the same WebAuthn-backed flow the clients expect.
Does Vaultwarden support Bitwarden Send (encrypted file and text sharing)?
Yes. Bitwarden Send — the time-limited encrypted text and file sharing feature — works on Vaultwarden. The clients use the same Send API endpoints, and the Vaultwarden server implements them. Recipients open the link in any browser. No Bitwarden account needed on their end.
Does Vaultwarden have audit logs?
Partially. Vaultwarden has added organization event logging in recent releases, covering common events like login attempts, vault access, and member changes. The depth is not at full parity with Bitwarden Enterprise. For a team doing standard access tracking, it covers the common cases. For strict regulatory logging requirements, evaluate carefully.
Does Vaultwarden support SSO (SAML / OIDC)?
Not at full parity with Bitwarden Enterprise. Vaultwarden supports OIDC-based SSO through community-contributed builds and some configuration work, but full SAML 2.0 federated SSO is not a first-class feature. Teams that require SAML SSO with their identity provider should evaluate Bitwarden Enterprise's self-hosted offering instead.
Can my team share passwords on Vaultwarden?
Yes. Vaultwarden supports organizations and shared collections — the same model Bitwarden uses for team password sharing. Each user has a personal vault and can be a member of one or more organizations with role-based access. Sharing works the way it does in Bitwarden Teams: create a collection, assign members, share items.
How does Vaultwarden compare to KeePassXC?
KeePassXC is a local file-based password manager — your vault is a single .kdbx file you sync yourself. Vaultwarden is a server with a sync API and clients across all platforms. KeePassXC is simpler and has no server to run. Vaultwarden gives you Bitwarden's UX, sharing, and team features in exchange for the operational overhead.
How does Vaultwarden compare to Passbolt?
Both are self-hosted team password managers. Passbolt is purpose-built for teams from the start with a different UX and PGP-based access control. Vaultwarden is for teams that want Bitwarden's specific UX and clients. If your team already uses Bitwarden, Vaultwarden is the lower-friction migration. Passbolt is a separate decision worth its own evaluation.
How many users can a single Vaultwarden instance handle?
Comfortably 100+ users on modest hardware. The bottleneck is usually disk for attachments and database I/O at peak sync, not CPU or RAM. Real-world deployments report 500+ users on a single instance. Above a few hundred users, the conversation shifts to redundancy and high availability — different problem from raw throughput.
What if Daniel García stops maintaining Vaultwarden?
A realistic risk worth thinking about. The project is open source under AGPL-3.0, so the code stays available. The active maintainer pool includes people beyond the original author. If maintenance slowed, your existing instance keeps working. At the worst case, the migration path back to Bitwarden's own server is straightforward — your data is in standard Bitwarden format.
Could Bitwarden break the API and lock Vaultwarden out?
Possible but unlikely. One Vaultwarden maintainer is employed by Bitwarden Inc, the protocol is documented, and the client apps need stable behaviour across client versions. A deliberate API break would harm Bitwarden's own self-hosting customers too. If it happened, Vaultwarden would adapt quickly — that's the value of an active maintainer pool.
What to do this week
If you're one person on Bitwarden Premium, do nothing. The $19.80/year price increase is annoying, not a switching trigger.
Vaultwarden hosted by anyone — including us — costs more than $19.80/year for a single user. Don't make work for yourself.
If you're a team of 5+ on Bitwarden Teams, run the math at your current headcount and at the headcount you expect twelve months from now. If the saving over a 24-month horizon is meaningful relative to the migration effort (which is small — same clients), the move is worth scoping properly.
If you decide to test it, the lowest-risk path is to start a 7-day free trial with a single user account — your own — on a managed Vaultwarden instance. Run it as your daily driver alongside your existing Bitwarden vault for a week. Migrate the team only if the trial confirms the math. Card failed during the trial? We don't delete your data. We email you and wait.