Managed Vault Hosting: The Complete Guide to Secure Secrets Management
TLDR - Quick Answer
Vault is a powerful, identity-based secrets and encryption management system. It secures, stores, and strictly controls access to tokens, passwords, certificates, and API keys.
Choosing Managed Vault Hosting gives you immediate value without the administrative overhead:
Centralized Security: Store all your sensitive credentials in one secure location instead of scattering them across plain text configuration files.
Dynamic Secrets: Generate temporary, highly restricted database credentials on the fly and revoke them automatically when a task finishes.
Encryption as a Service: Encrypt application data in transit and at rest without writing complex, error-prone cryptography code.
Zero Setup Time: Skip the complex manual configuration entirely. Launch a secure, highly available Vault environment instantly.
Introduction
Managing secrets is exceptionally difficult. If you build software, you constantly handle API keys, database passwords, and TLS certificates. Storing these credentials in code repositories or plain text .env files is a major security risk. Hardcoded secrets inevitably lead to devastating breaches. You need a central, secure place to lock them down.
Vault solves this problem perfectly. It treats security as a core part of your infrastructure. But running it yourself is a second job. Configuring storage backends, handling high availability, and managing unseal keys takes hours of careful work. One simple mistake can lock you out of your own data or expose your sensitive systems to the public internet.
You do not need to become a full-time system administrator to secure your applications. With DANIAN acting as your invisible infrastructure team, you get all the power of Vault without the maintenance headache. We handle the complex server work behind the scenes. You simply use the software.
What is Vault?
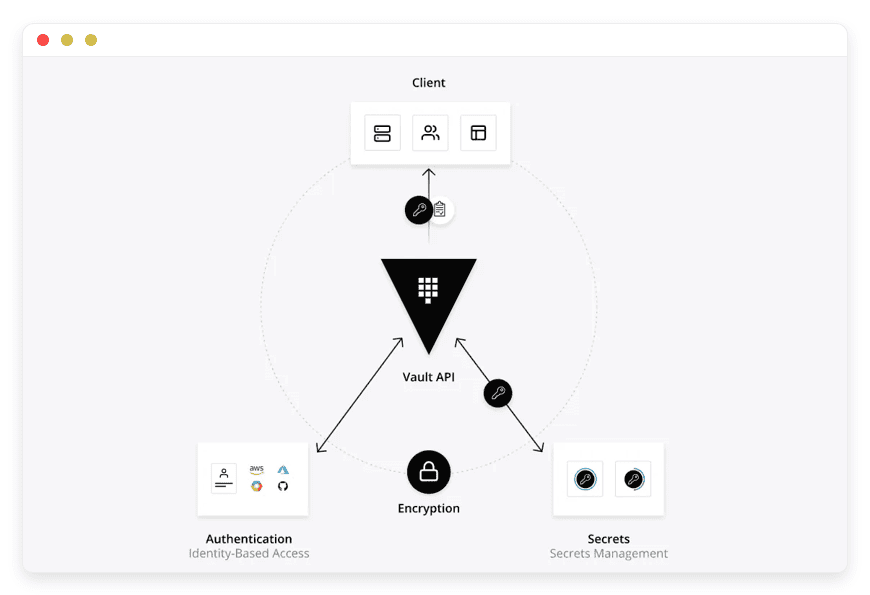
Vault is a popular open-source tool created by HashiCorp. It provides a unified, secure interface to manage secrets and protect sensitive data. Instead of scattering passwords across different applications, you store them securely in Vault. Your applications then authenticate and ask Vault for the specific credentials they need to function.
Vault relies entirely on identity-based access. Before any user, script, or machine gets a secret, they must prove who they are. Vault connects natively with platforms like GitHub, LDAP, and various cloud identity providers to verify these credentials. Once verified, Vault grants access based on strict, clearly defined policies.
It also acts as a powerful encryption engine. It can encrypt data for your applications, generate unique passwords dynamically, and issue short-lived certificates. Everything is logged automatically. This gives you a crystal-clear audit trail of who accessed what and exactly when it happened.
Why is it trending?
Vault is trending because manual security no longer works. Modern software architectures are highly dynamic. Microservices start up, do their specific work, and shut down in minutes. Static, unchanging passwords fail in this fast-paced environment. Vault provides zero-trust security. It assumes no network or application is safe by default. Every single request for data requires strict authentication. This approach keeps systems secure even if a network perimeter is compromised.
Why Choose Vault?
Choosing Vault fundamentally changes how your engineering team handles security. It completely removes the need to share database passwords over chat applications or email. You replace static, never-changing credentials with dynamic, short-lived tokens that expire automatically.
Hosting Vault gives you ultimate control over your security posture. You gain the freedom of a massive open-source ecosystem. Thousands of developers actively contribute to its plugins and integrations. It natively supports almost every major database, identity provider, and message queue on the market today.
When you invest in Hosting Vault, you centralize your trust. Instead of auditing ten different tools to see who accessed your database, you check a single, unified audit log. It enforces strict access policies across your entire technology stack. You write a security rule once, and it applies universally. This level of control drastically reduces human error and keeps your applications secure by design.
Key Features of Vault
Vault is packed with powerful features that replace fragmented, insecure security tools. Below is a deep dive into the core functions that make it the industry standard for secure infrastructure.
Key/Value (KV) Secrets Engine
This is the simplest and most common way to use Vault. You store static secrets like third-party API tokens or external service passwords in a secure directory structure. Vault encrypts these secrets immediately before saving them to disk. The latest version of the KV engine supports detailed secret versioning.
Workflow Benefit: Your developers stop putting API keys directly into source code. During runtime, your application simply asks Vault for the key. If you accidentally overwrite a critical password, you can instantly restore the previous version. If you need to rotate a compromised key, you change it once in Vault. All your applications pull the new key automatically without requiring complex code redeploys.
Dynamic Database Credentials
Static database passwords are a massive security risk. Vault solves this by generating database credentials dynamically on demand. It supports databases like PostgreSQL, MySQL, MongoDB, and Redis. When an application needs to talk to the database, Vault connects to the database and creates a unique username and password.
Workflow Benefit: You assign a strict Time-To-Live (TTL) to these generated credentials. If the TTL is set to one hour, Vault automatically tells the database to delete that specific user after exactly one hour. If an attacker manages to steal the password, it becomes completely useless very quickly. You never have to manually rotate shared database passwords again.
Encryption as a Service (Transit Engine)
Writing custom cryptography code is incredibly dangerous. A small implementation mistake can leave sensitive data exposed. Vault’s Transit Secrets Engine handles complex cryptographic functions for you securely. Your application sends plain text data to Vault via a simple API call. Vault encrypts it and returns the secure ciphertext.
Workflow Benefit: Your developers do not need to understand AES-GCM, key derivation, or manual key rotation. Vault manages the keys and all the complex math safely. You can easily encrypt user emails or personal messages before storing them in your primary database. If someone steals your database dump, they only get unreadable, useless ciphertext.
Data Tokenization (Transform Engine)
Sometimes you need to store data but hide specific parts of it. A common example is showing only the last four digits of a credit card number. The Transform engine masks or tokenizes sensitive data using Format-Preserving Encryption (FPE).
Workflow Benefit: You can safely share production databases with your internal testing teams. Vault automatically masks the sensitive Personally Identifiable Information (PII) before the testing team ever sees it. You maintain strict security while allowing your developers to test applications with realistic data structures and formats.
Identity and Access Control (ACL Policies)
Vault uses the HashiCorp Configuration Language (HCL) to write clear, human-readable security policies. These policies dictate exactly which paths a user or machine can access. Vault operates on a strict deny-by-default mechanism. If a policy does not explicitly grant access, the request is instantly rejected.
Workflow Benefit: You map your organizational structure directly to Vault policies. A junior developer gets a policy that only allows reading secrets in the staging environment. A senior engineer gets a policy to write secrets to production. This granularity ensures no single identity has complete access to your entire infrastructure.
Public Key Infrastructure (PKI) Engine
Manually tracking when internal SSL/TLS certificates expire leads to unexpected website outages. Vault acts as a highly secure Private Certificate Authority (CA). It can generate root certificates, intermediate certificates, and issue signed TLS certificates to your internal microservices automatically.
Workflow Benefit: Your internal tools can communicate securely using mutual TLS (mTLS) without you ever manually generating a single certificate file. Vault automates the entire lifecycle. It issues short-lived certificates that expire in days or hours. This completely eliminates the risk of long-lived, compromised certificates residing on your servers.
Detailed Audit Devices
Security requires visibility. Vault logs every single request made to its API. It records who authenticated, what specific policy they used, and exactly what secret they accessed or modified. It supports multiple audit devices simultaneously, such as local files or remote Syslog servers.
Workflow Benefit: Security audits become remarkably simple. You can send these detailed logs to a central monitoring system. Vault securely hashes sensitive fields in the logs, so passwords are never written in plain text. If a specific application starts requesting a database password a hundred times a second, your team can spot the anomaly and investigate it immediately.
SSH Secrets Engine
Managing SSH keys for dozens of Linux servers is a well-known security nightmare. Developers copy their public keys to machines and often forget to remove them later. Vault acts as a centralized SSH Certificate Authority. It issues signed SSH certificates or One-Time Passwords (OTP) for server access.
Workflow Benefit: You completely eliminate static authorized_keys files from your servers. A developer authenticates with Vault and requests an SSH certificate valid for only two hours. They use this short-lived certificate to log into the production server securely. After two hours, their access expires automatically. No cleanup is required.
Solutions per Industry
Vault adapts flawlessly to the specific security requirements of completely different business environments. Here is how nine distinct industries use this powerful software to solve complex infrastructure problems.
1. eCommerce Stores
eCommerce platforms handle massive amounts of sensitive customer data, shipping addresses, and payment information. During high-traffic events like Black Friday, they need to scale application web servers up and down rapidly to handle the load.
The Problem: Copying static database passwords to hundreds of temporary web servers creates a massive security vulnerability.
The Solution: Vault provides dynamic database credentials. As new shopping cart servers start up, they request temporary database access from Vault. Vault grants unique, short-lived passwords for each server. When the traffic spike ends and the servers shut down, Vault revokes the access automatically. The eCommerce store completely avoids the risk of leaving permanent database credentials scattered across destroyed servers.
2. Software Development Agencies
Agencies build, deploy, and maintain custom applications for dozens of different clients simultaneously. Managing third-party API keys, server root passwords, and staging environment credentials for multiple clients creates administrative chaos.
The Problem: Developers often share client credentials in chat applications, leading to accidental leaks and compromised client data.
The Solution: The agency sets up Vault with strict Access Control Lists (ACLs). They create a specific, isolated path for each individual client. Developers only receive access to the secrets for the exact projects they are actively working on. When a developer leaves the agency, the administrator simply removes their identity from Vault. Their access to every single client secret is revoked instantly and permanently.
3. Educational Institutions
Universities and colleges manage a vast network of students, faculty members, and administrative staff. They need to protect sensitive student records and private research data while allowing open access to general learning resources.
The Problem: Storing student grades and financial aid information in plain text databases leaves institutions vulnerable to severe data breaches.
The Solution: The university IT department uses Vault's Transit Engine to encrypt student records before storing them in the main database. They tie Vault authentication directly to the university's existing Active Directory system. Faculty members authenticate with their standard university login to decrypt specific student grades. Students only have restricted access to their own specific records.
4. FinTech Startups
Financial technology companies process highly sensitive transactions daily. They interact with banking APIs, payment gateways, and global financial networks. Security is not just a feature; it is the entire foundation of their business model.
The Problem: Storing credit card numbers and bank account routing details in plain text can destroy a company overnight if a breach occurs.
The Solution: FinTech applications use Vault’s Transform Engine to tokenize incoming credit card data. The application sends the real card number to Vault, and Vault returns a masked token. The application stores this safe token in the database. Vault also maintains incredibly strict audit logs, recording exactly which internal service requested the real card number for payment processing.
5. Gaming Studios
Modern multiplayer games rely on hundreds of distributed servers to handle player matchmaking, game state synchronization, and in-game purchases. These servers spin up dynamically based on current player counts.
The Problem: Distributing API keys to temporary game server instances is risky. If a malicious player extracts a key from a server, they can manipulate the game economy.
The Solution: The game studio uses Vault to issue short-lived API tokens for every new match server. The server authenticates with Vault using AppRole, receives a token valid only for the duration of the match, and uses it to update player scores securely. When the match ends, the token expires automatically. The studio protects its game economy effortlessly.
6. SaaS Platforms
Software-as-a-Service businesses often employ multi-tenant architectures. They host data for thousands of different companies on the same physical database infrastructure.
The Problem: A simple code bug could accidentally expose one tenant's secret API keys (like their Twilio or Stripe credentials) to a completely different tenant.
The Solution: The SaaS platform uses Vault to create strict, logically isolated boundaries between tenants. Each customer gets a dedicated secret path inside Vault. The core application dynamically assumes a highly restricted role based on which user is currently logged in. It can only ever fetch secrets belonging to that specific tenant, ensuring total data isolation.
7. Media & Broadcasting
Streaming services and media companies deliver digital content globally. They must protect their premium video streams, secure Digital Rights Management (DRM) keys, and handle massive viewer spikes during live events.
The Problem: If a DRM key or a live broadcasting credential is leaked, unauthorized users can pirate premium content instantly.
The Solution: Media companies use Vault to store and rotate DRM keys automatically. During a live sports broadcast, Vault issues temporary streaming credentials to edge delivery servers. These credentials automatically expire the moment the broadcast concludes. The company protects its highly valuable digital assets without manual intervention.
8. Logistics & Supply Chain
Global shipping companies manage thousands of connected delivery trucks, warehouse scanners, and automated sorting machines. These IoT (Internet of Things) devices need to send real-time tracking data back to central servers.
The Problem: Embedding permanent authentication tokens into physical delivery trucks is incredibly dangerous. If a truck is stolen, the physical hardware contains the keys to the corporate network.
The Solution: The logistics company issues unique, machine-based identities to each truck using Vault. When a truck starts its engine, the onboard computer authenticates with Vault using its hardware signature. Vault provides a temporary token valid only for that specific delivery shift. If the hardware is compromised, the token expires quickly, protecting the central tracking system.
9. Data Analytics Firms
Data science teams ingest massive datasets from various sources to run complex machine learning models. They constantly query production databases to gather fresh information.
The Problem: Giving a data scientist permanent, unrestricted read access to a production database is risky. They might accidentally run an unoptimized query that crashes the live application.
The Solution: The analytics firm uses Vault to manage database access securely. When a data scientist needs to run a batch job, they authenticate with Vault and request credentials for a read-only database replica. Vault generates a username and password valid for just six hours. The data scientist runs their models securely. Once the job finishes, the database access is revoked automatically.
Vault vs Other Softwares
When evaluating secure secrets management, it helps immensely to see how Vault compares directly to other software applications available in the market.
| Feature | Vault | Doppler | CyberArk Conjur |
Core Focus | Identity-based dynamic secrets and encryption | Developer-focused environment variable sync | Enterprise privileged access management |
Dynamic Secrets | Yes, creates temporary, short-lived credentials | No, primarily syncs static secrets across apps | Yes, handles dynamic access well |
Encryption as a Service | Yes (Powerful Transit and Transform engines) | No | Limited, mostly focuses purely on access control |
Open-Source Base | Yes | No | Yes (Conjur open-source version) |
Setup Complexity | High (if not fully managed) | Low | Very High |
Target Audience | Infrastructure teams, security engineers, developers | Frontend and backend app developers needing quick sync | Compliance officers and legacy enterprise systems |
Vault hits the perfect middle ground for modern engineering teams. It offers the deep technical capabilities of complex legacy systems while maintaining a clean, modern API that developers actually love to use.
Use Cases and Applications
Here are practical, everyday examples of how highly technical teams use Vault to improve their workflows.
Securing CI/CD Pipelines
Continuous Integration systems like GitHub Actions or GitLab CI need deep access to your infrastructure to deploy code. Storing production deployment keys directly inside the CI tool is risky. Instead, the CI pipeline authenticates with Vault using a short-lived token. It fetches the required deployment secrets, pushes the code, and forgets the secrets entirely. Your deployment keys remain safely inside Vault.
Infrastructure as Code (Terraform Integration)
When you use tools like Terraform to build cloud infrastructure, you often need to provide database passwords or API tokens to configure new servers. The Terraform Vault provider allows you to pull these secrets dynamically during the run. The secrets never touch your local hard drive and are never accidentally committed to your state files.
Automated Machine Authentication (AppRole)
Machines need to prove their exact identity just like human users do. Vault uses the AppRole authentication method specifically for this purpose. When your automated script or application starts, it presents a secure RoleID and a SecretID directly to Vault. Once verified successfully, Vault issues a temporary token. The application uses this precise token to fetch its required API keys. This ensures only your verified code can ever access your highly sensitive secrets.
Application Configuration Reloading
Applications often crash when database passwords change because they hold onto stale connections. You can use Vault Agent alongside your application. Vault Agent quietly fetches new database credentials before the old ones expire. It writes them securely to memory and sends a signal to your application to reload its configuration seamlessly. You achieve zero-downtime secret rotation.
How DANIAN Helps
Hosting Vault is incredibly powerful, but configuring it perfectly requires deep system administration knowledge. You have to handle complex storage backends, manage seal and unseal mechanics securely, and configure high availability routing perfectly. We act as your quiet, highly capable enabler. We handle the complex server mess; you get all the glory of a secure application.
Here is exactly how DANIAN makes Vault completely effortless for your team:
Fully Managed: We handle the entire hosting process from start to finish. Our experienced team manages everything from the initial complex setup to regular updates, security patches, and constant performance monitoring. Your software is always optimized perfectly without you having to lift a single finger.
Backup & Monitoring: Automated daily backups are configured automatically and stored securely offsite. If you ever need to roll back to a previous state, we provide a simple, incredibly fast one-click restore process.
SSL & Firewall: Secure by default is our core philosophy. With cybersecurity threats constantly on the rise, we take your security seriously. From automated TLS certificate updates to proactive traffic monitoring and strict firewall rules, we make sure your environment is secure 24/7.
Updates: Critical security patches and completely new versions of Vault are applied smoothly without your direct intervention. You always have the latest powerful features and essential security fixes immediately.
24/7 Monitoring: Infrastructure issues are detected instantly and often resolved completely before you even notice them. We watch the system resources carefully so you do not have to worry about memory spikes.
Guaranteed Performance: Application downtime can be highly detrimental to your business reputation. With our scalable, robust infrastructure, we ensure consistent, blazing-fast performance even as your engineering team grows or your API request volume spikes dramatically.
7-Day Free Trial: There is absolutely no financial risk to try our platform. See the incredible benefits of a fully managed system yourself before committing.
Less setup time, more productive development. Affordable from the very start, with real, human help when you actually need it.
How to Get Started
Getting your own highly secure secrets manager takes less than five minutes. You do not need to configure complex servers or edit confusing configuration files manually.
Step 1: Visit danian.co and sign up for a quick account.
Step 2: Select Vault from our extensive software catalog.
Step 3: Relax completely while DANIAN gets your software running instantly.
FAQ
What is the precise difference between static and dynamic secrets in Vault?
Static secrets are fixed text strings, exactly like an API key for a third-party payment gateway. You store them manually in Vault, and they only change when a human manually updates them. Dynamic secrets are generated by Vault entirely on the fly. When your application needs database access, Vault creates a temporary, fully functional username and password. It then deletes that user automatically from the database when it is no longer needed.
Do I need to know complex cryptography to use Vault effectively?
No, you do not. That is the true beauty of the Transit Secrets Engine. Vault handles all the complex math, secure salt generation, and advanced cipher algorithms internally. Your application simply sends plain text via an API call and receives encrypted text back. You interact strictly with simple, developer-friendly REST APIs.
What happens securely if the Vault server restarts?
By design, Vault starts in a highly secure "sealed" state. It absolutely cannot read its own storage until it is unsealed using multiple cryptographic keys. In a self-hosted environment, this requires annoying manual intervention or highly complex auto-unseal configurations. With Managed Vault Hosting, we handle the complex unseal process automatically and securely behind the scenes. This ensures your applications never lose access to their critical secrets after a system reboot.
Can I restrict access strictly to specific secrets?
Yes. Vault uses HashiCorp Configuration Language (HCL) to let you define highly strict access policies. You can easily write a policy that explicitly states "Developer A can only read secrets inside the staging folder, but absolutely cannot update or delete them." Vault enforces these rules rigidly and consistently across all authentication methods.
Is the open-source version of Vault fully featured for teams?
Yes, absolutely. The open-source version includes the KV store, dynamic secrets for databases, transit encryption, and extensive identity integrations. It provides everything a highly technical team needs to secure a complex application stack effectively.
How exactly do automated applications authenticate with Vault?
Applications can authenticate securely using several different methods. The most common is AppRole, which acts exactly like a highly secure machine-based username and password. If you use cloud platforms, Vault can also verify the precise identity of an application using the cloud provider's native identity systems securely.
Can Vault effectively manage internal TLS certificates?
Yes. Vault has a robust, highly capable Public Key Infrastructure (PKI) secrets engine. It can securely generate internal Root and Intermediate Certificate Authorities. You can use it to issue TLS certificates automatically for your internal network, ensuring all communication between your internal servers is heavily encrypted and safe from interception.
Does DANIAN pricing include the Vault license?
Vault is open-source software, so there are absolutely no expensive software licensing fees to pay for the core features. You are paying strictly for the highly reliable hosting infrastructure, automated backups, and expert management we provide to keep your instance running perfectly.
Conclusion
Vault completely transforms how your engineering team handles complex application security. Moving away from scattered plain text passwords to a centralized, identity-based dynamic secrets system protects your business from devastating data breaches. It provides unparalleled organizational control, deeply detailed audit logs, and highly powerful encryption tools that fundamentally simplify your developers' workflows.
You deserve a secure, fully functional infrastructure environment without the heavy system administration burden. Let us handle the complex server configurations so your team can focus entirely on building amazing, secure software faster than ever.
Experience the incredible power of fully managed open-source software today.