Managed Keycloak Hosting: The Modern Standard for Identity Management
TLDR - Quick Answer
Keycloak is the definitive open-source Identity and Access Management (IAM) solution. It acts as a centralized authorization server that secures your applications, microservices, and APIs with little to no coding required.
Why Managed Keycloak Hosting?
Instant Security: Out-of-the-box Single Sign-On (SSO), Two-Factor Authentication (2FA), and Social Login.
Standard Compliance: Native, strictly compliant support for OpenID Connect (OIDC), OAuth 2.0, and SAML 2.0.
Centralized Control: Manage users, roles, sessions, and clients from a single, unified dashboard.
Zero Maintenance: No need to manage Java Virtual Machines (JVM), relation databases, or complex upgrades.
Developer Focus: Offload the burden of security infrastructure so you can build features, not login forms.
Introduction
Building an authentication system from scratch is one of the riskiest decisions a development team can make. It is also a massive drain on resources. To build a secure login system today, you cannot simply check a username and password against a database table. You must handle password hashing, salt rotation, session management, token encryption, brute-force protection, and an endless list of emerging security vulnerabilities (CVEs).
Most developers and architects prefer Keycloak because it solves these problems instantly. It provides a robust, battle-tested login system that you can plug into any application—whether it's a monolithic legacy app or a modern mesh of microservices.
But running it yourself is a second job. Keycloak is a powerful beast. It is a Java-based application that requires a configured relational database (like PostgreSQL), specific memory tuning for the JVM, careful handling of reverse proxy headers, and rigorous security patching. If your IAM server goes down, nobody logs in. Your business effectively stops.
DANIAN acts as your invisible infrastructure team. We handle the complex server requirements, the database provisioning, the security patches, and the uptime monitoring. You get a fully functional, high-performance authentication server ready to connect to your apps in minutes.
What is Keycloak?
Keycloak is an open-source Identity and Access Management (IAM) solution aimed at modern applications and services. It was originally developed by the JBoss community and is now maintained under the stewardship of Red Hat. It is the upstream project for Red Hat Single Sign-On (RH-SSO), meaning it contains the latest features and cutting-edge developments in identity security.
At its core, Keycloak acts as a gatekeeper. Instead of your application handling user credentials directly, it redirects users to Keycloak to log in. Once authenticated, Keycloak tells your app, "This user is valid, and here are their permissions," using cryptographically signed tokens.
Recently, Keycloak underwent a massive architectural shift, migrating its underlying container from WildFly to Quarkus. This change has made Keycloak faster, lighter, and more cloud-native, significantly reducing startup times and memory footprint. This modern architecture makes it ideal for containerized environments and high-performance hosting.
Why is it trending?
Modern software architecture has shifted toward microservices, distributed apps, and composable enterprises. You cannot have a separate user database for every single service—that leads to "identity silos" and a terrible user experience. Keycloak centralizes identity. It allows a user to log in once and access different applications without re-entering credentials. It is the industry standard for decoupling identity from application logic, allowing developers to treat "Identity" as a service rather than a code module.
Why Choose Keycloak?
The primary reason developers choose Keycloak is freedom and capability. Many proprietary authentication services charge per "Monthly Active User" (MAU). As your app grows, your bill creates a massive overhead, effectively penalizing you for acquiring more customers.
With Hosting Keycloak, the economics are different. The software is free and open-source. You pay for the server resources—CPU and RAM—not the number of users in your database. You can have 100 users or 100,000 users; if the server handles the load, your price remains the same.
Additionally, Keycloak offers feature parity with expensive enterprise tools. It supports the same heavy-lifting protocols—OpenID Connect, OAuth 2.0, and SAML 2.0—used by the banking, healthcare, and government sectors. It allows you to own your identity data completely, ensuring you can export your users and configurations at any time.
Key Features of Keycloak
Keycloak is packed with features that replace months—or even years—of custom development. It is designed to be comprehensive, covering almost every authentication use case imaginable.
Single Sign-On (SSO)
This is the flagship feature. Users authenticate with Keycloak rather than individual applications. This means your users log in once to access your web apps, mobile apps, and backend services. When they log out, they are signed out everywhere. This is crucial for security and user experience. If an employee leaves your company, you disable their account in one place (Keycloak), and they instantly lose access to all connected systems.
Identity Brokering and Social Login
You don't always want to manage passwords. Keycloak can use external identity providers. You can enable login via Google, Facebook, GitHub, LinkedIn, Twitter, or Microsoft with simple configuration. Keycloak acts as a broker:
The user clicks "Login with Google."
Keycloak handles the handshake with Google.
Google verifies the user.
Keycloak creates a session and passes a standard token back to your app.
Your app never sees the complexity; it just sees a logged-in user.
User Federation and LDAP/AD Integration
If you already have a user database, Keycloak can connect to it. It has built-in support for LDAP and Active Directory. It doesn't just "read" these databases; it can sync credentials and roles.
Kerberos Integration: It supports automatic authentication if users are already logged into a Windows domain.
Mappers: You can map LDAP attributes (like "Department" or "Manager") directly into the tokens your application receives, allowing you to build logic based on existing corporate data.
Fine-Grained Authorization Services
Beyond just "who are you" (Authentication), Keycloak handles "what can you do" (Authorization). It allows you to define granular policies and permissions for your resources.
Role-Based Access Control (RBAC): Assign roles like admin, editor, or viewer.
Attribute-Based Access Control (ABAC): Create policies like "Users can only access this resource if they are in the IT department and it is during business hours."
Keycloak acts as a Policy Decision Point (PDP), centralizing authorization logic so you don't have to hard-code complex if/else statements in your app.
Strong Authentication and MFA
Keycloak supports Two-Factor Authentication (2FA) and Multi-Factor Authentication (MFA) out of the box.
TOTP/HOTP: Compatible with Google Authenticator, Microsoft Authenticator, and FreeOTP.
WebAuthn/Passkeys: Support for passwordless login using biometric readers (TouchID, FaceID) or hardware keys like YubiKeys.
Step-up Authentication: You can configure policies where a user can log in with a password for general access, but must provide 2FA to access sensitive areas (like billing settings).
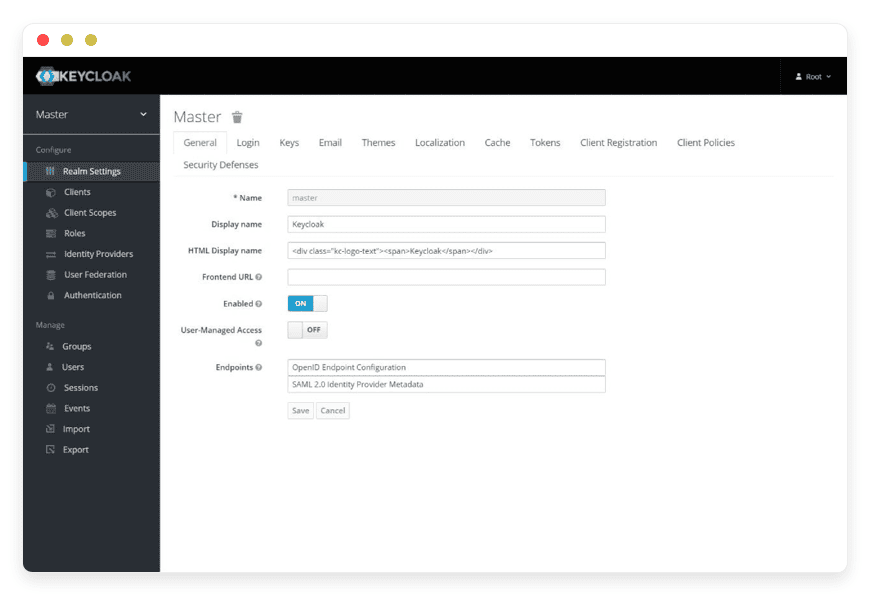
Comprehensive Admin Console
Managing users is often an afterthought in custom builds. Keycloak provides a comprehensive web-based GUI. Administrators can:
Search and manage thousands of users.
Impersonate users to troubleshoot issues.
Force password resets via email.
View all active user sessions and kill specific sessions instantly.
Configure email templates for password recovery and verification.
Service Provider Interfaces (SPIs) & Extensibility
Keycloak is designed to be customized. If the out-of-the-box features don't fit your needs, you can write custom code (SPIs) to extend it.
User Storage SPI: Connect to a custom legacy database that isn't SQL or LDAP.
Protocol Mapper SPI: Change how tokens are generated.
Event Listener SPI: Push audit logs to external systems like Splunk or Datadog whenever a user logs in or fails authentication.
Account Management Console
Keycloak includes a built-in self-service portal for your end-users. They can log in to their own profile to:
Update their email and basic profile data.
Change their password.
Set up their 2FA/MFA devices.
View their active sessions and sign out of devices they don't recognize.
View which applications have access to their data.
This significantly reduces support tickets for password resets and profile updates.
Solutions per Industry
Keycloak is industry-agnostic, but its powerful feature set solves specific, critical problems for different verticals. Here is how various industries utilize Managed Keycloak Hosting.
1. SaaS and Tech Startups (Multi-Tenancy)
The Pain: SaaS platforms often serve multiple business clients (tenants). Each client wants their own settings, their own admins, and sometimes their own branding. Building a "multi-tenant" auth system is incredibly complex and prone to data leaks between tenants.
The Solution: Keycloak solves this with Realms. A startup can launch a single Keycloak instance and create a separate Realm for every customer.
Isolation: Users in Realm A cannot log in to Realm B.
Customization: Realm A can use "Login with Google," while Realm B forces "Active Directory Integration."
Speed: The startup can onboard a new enterprise client in minutes by simply spinning up a new Realm, rather than deploying new infrastructure.
2. Retail and eCommerce
The Pain: In eCommerce, friction kills conversion. If a user has to fill out a long registration form to buy a product, they abandon the cart. However, the store still needs to secure customer data and maintain order history.
The Solution: Keycloak enables Social Login and Anonymous Sessions.
Social Boost: Users click "Buy with Apple" or "Login with Facebook," creating an account instantly without typing.
Unified Profile: If the retailer has a web store and a mobile loyalty app, Keycloak provides the SSO bridge. A user logs into the app, and when they visit the mobile web store, they are automatically logged in, increasing the likelihood of purchase.
3. Financial Services and FinTech
The Pain: Banks and FinTech apps face strict regulatory requirements (like PSD2 in Europe). They need "Strong Customer Authentication" (SCA). A simple password is never enough, but nagging users for 2FA on every login ruins the experience.
The Solution: Keycloak supports Adaptive Authentication and Step-Up Auth.
Scenario: A user logs in to view their balance. Keycloak checks the device signature. If it's a known device, it allows access with just a password.
The Pivot: The user tries to transfer $1,000. The application requests a "step-up." Keycloak detects the higher security requirement and forces the user to provide a 2FA code or a biometric scan before issuing the token required for the transfer API. This balances usability with maximum security.
4. Healthcare and MedTech
The Pain: Healthcare applications handle sensitive patient data. They require strict access logs and granular permission controls. A doctor should see patient records; a receptionist should only see scheduling.
The Solution: Keycloak’s Fine-Grained Authorization and Audit Logging.
Role Mapping: Keycloak assigns roles like doctor, nurse, or admin. The application relies on these roles to render the UI.
Traceability: Every single login, failed attempt, and token issuance is logged. These logs can be exported to audit systems to prove compliance with internal data governance policies. Keycloak ensures that access is not just granted, but documented.
5. Government and Public Sector
The Pain: Government agencies often have massive legacy systems running on old mainframes or LDAP directories, but they need to offer modern digital services to citizens (web portals, mobile apps).
The Solution: Keycloak acts as the Identity Bridge.
The Bridge: Keycloak connects to the legacy LDAP databases via User Federation.
The Modern Front: It presents a modern OpenID Connect interface to the new web portals.
Result: Citizens can use their existing government IDs to log in to modern apps, and the agency doesn't have to migrate millions of user records from their secure legacy systems.
6. Internet of Things (IoT) and Manufacturing
The Pain: Smart devices (thermostats, industrial sensors, factory robots) need to authenticate to send data to the cloud. These devices often don't have keyboards or screens, making standard login forms impossible.
The Solution: Keycloak supports OAuth 2.0 Device Flow.
The Flow: The device connects to Keycloak and gets a code. The user visits a URL on their phone or laptop, enters the code, and authorizes the device.
Token Management: Keycloak issues a long-lived offline token to the device. If the device is stolen, the admin can revoke the token centrally in Keycloak, instantly cutting off the device's access to the cloud API.
7. Education and Universities
The Pain: Universities are small cities. They have thousands of students, faculty, and temporary researchers. They have hundreds of apps: Library systems, dorm Wi-Fi, grading portals, and research databases. Managing access for this churning population is a nightmare.
The Solution: Keycloak’s Identity Brokering and SAML Support.
EduRoam/Shibboleth: Keycloak can broker authentication from other universities using SAML. A visiting researcher from University A can log in to the library portal of University B using their home credentials.
Lifecycle Management: When a semester ends, automating the expiry of student sessions across all apps becomes a single-click operation in the Keycloak admin console.
Keycloak vs Other Software
The market is full of authentication providers. The main distinction is between "SaaS/Proprietary" (Auth0, Okta, Firebase Auth) and "Open Source" (Keycloak).
| Feature | Keycloak (Open Source) | Proprietary SaaS Auth |
| Cost Model | Flat hosting fee (Unlimited Users). You pay for the container size. | Pay per Monthly Active User (MAU). Costs skyrocket as you scale. |
| Data Sovereignty | You own the database. You can export the full SQL dump. | Data is locked in their cloud. Exporting hashes is often difficult or impossible. |
| Code Access | Full Source Code. You can audit security and write custom SPIs. | Closed Source. You trust their "black box." |
| Protocols | Native OIDC, SAML, OAuth 2.0, Docker Registry Auth. | Often limited by pricing tier (e.g., SAML is usually "Enterprise Only"). |
| Customization | Full control over HTML/CSS (FreeMarker templates) and logic. | Full control over HTML/CSS (FreeMarker templates) and logic. |
The Verdict: Proprietary tools are excellent for prototypes. Keycloak is the superior choice for long-term scalability, cost control, and data ownership.
Use Cases and Applications
Keycloak is versatile. Here are practical ways developers deploy it:
Securing Microservices Architectures: In a Kubernetes environment, use Keycloak as the centralized auth server. An API Gateway (like Nginx or Kong) sits in front of your services. It checks with Keycloak to validate the Access Token before letting traffic through.
Internal Employee Portals: Companies often have 20+ internal tools (Jenkins, Grafana, CRM, Wiki). Instead of creating 20 usernames, connect them all to Keycloak. Employees use their single corporate login to access everything.
Mobile App Authentication: Seamless integration with Android and iOS apps using the Keycloak client adapters. It handles the complexity of "Refresh Tokens," ensuring users stay logged in on their phones without compromising security.
API Security & Monetization: If you sell access to an API, you can use Keycloak to issue Client Credentials tokens. You can track which client is using the API and revoke access if they stop paying, without changing code.
How DANIAN Helps
We act as the "Quiet Enabler." We handle the mess; you get the glory. Running Keycloak in production requires more than just downloading a zip file. It requires high availability, database management, and security hardening.
Fully Managed: We handle the hosting. Our team manages everything from the initial Java environment setup to database connections. We optimize the JVM heap size and thread pools to ensure your Keycloak instance runs smoothly under load.
Backup & Monitoring: We configure automated daily backups and store them securely off-site. If you delete a Realm by mistake, we can restore it. We monitor your server 24/7 for CPU spikes, memory leaks, or connectivity issues.
SSL & Firewall: Security is not optional for an Auth server. We include SSL certificates automatically. We also configure custom firewalls to block unauthorized access to your administration ports, ensuring only your team can access the console.
Updates & Patching: Identity software is a prime target for hackers. Keycloak releases frequent updates to patch vulnerabilities. We apply these updates so your authentication system remains secure against new threats without you having to manually migrate versions.
Guaranteed Performance: Downtime is detrimental to your business. If Keycloak is down, your entire business is down. With our scalable infrastructure, we ensure consistent performance. We use high-performance storage and dedicated resources to prevent "noisy neighbor" issues.
7-Day Free Trial: There is no risk. Spin up a Keycloak instance, connect it to your app, and see how easy it is to manage identity.
Less Setup, More Development. Affordable from the Start. Real Help When You Need It.
How to Get Started
Visit DANIAN: Create your account in seconds.
Select Keycloak: Find Keycloak in our one-click catalog.
Relax: We provision the PostgreSQL database, set up the container, configure the reverse proxy, and secure the endpoint.
Login: You receive the admin credentials. You can log in and start creating Realms immediately.
FAQ
Is Keycloak free to use?
Yes, the software itself is open-source and free (Apache License 2.0). You only pay for the hosting resources required to run it, or for the full management service which includes the hosting. There are no licensing fees per user.
Does Keycloak support Two-Factor Authentication (2FA)?
Yes. Keycloak has built-in support for Time-based One-Time Passwords (TOTP) utilizing apps like Google Authenticator, Microsoft Authenticator, or FreeOTP. It also supports WebAuthn for hardware keys.
Can I theme the login page?
Absolutely. Keycloak uses FreeMarker templates. You can fully customize the HTML and CSS of login pages, emails, and account consoles to match your brand identity perfectly. You can even run multiple themes for different tenants.
What is a "Realm" in Keycloak?
A Realm is a logical space where you manage a set of users, credentials, roles, and groups. Realms are isolated from one another. You can have multiple realms in one Keycloak instance (e.g., one Realm for "Customers" and a completely different Realm for "Employees").
Can I migrate if I am already hosting Keycloak elsewhere?
Yes. Keycloak has strong import/export features. You can export your current realm configuration (users, clients, roles) to a JSON file and import it directly into your DANIAN instance.
Does Keycloak support multi-tenancy?
Yes, via Realms. A single Keycloak instance can host hundreds of distinct Realms, allowing you to serve hundreds of different business clients securely from one installation.
How does Keycloak handle "Forgot Password" flows?
It handles them entirely. You configure your SMTP (email) server settings in Keycloak. When a user clicks "Forgot Password," Keycloak generates a secure, time-limited link and emails it to the user. Your application code does not need to handle this logic. DANIAN includes the SMTP with the Keycloak service by default.
Conclusion
Identity management is the backbone of modern applications. It is also the most critical security component you will ever deploy. A breach in your auth system is a breach of everything.
Don't waste time reinventing the wheel or struggling with the complexity of managing Java application servers, database connections, and security patches. Keycloak offers the enterprise-grade features you need—SSO, Social Login, User Federation, and Fine-Grained Auth—without the enterprise price tag.
DANIAN provides the invisible, robust infrastructure to keep it running smoothly, securely, and reliably. We let you focus on your code, while we ensure your users can always log in.